A clean audit report feels like a win.
Your Data Loss Prevention system passed. Regulators approved it. Internal teams move on.
But here’s the real question.
Is your sensitive data actually protected?
In most cases, the answer is no.
There is a clear gap between passing compliance audits and stopping real data exfiltration. Most companies don’t see it until it’s too late.
The Compliance Problem: You Passed, But You’re Still Exposed
Audits Focus on Documentation, Not Real Attacks
Compliance frameworks are built for verification, not defense.
Auditors check:
- Policies exist
- Controls are configured
- Systems are deployed
They do not test:
- Insider data theft scenarios
- Real-world bypass techniques
- Advanced exfiltration methods
Example:
- Audit question: “Do you block credit card data in emails?”
- Real risk: “Can an employee upload your entire client database to Google Drive?”
One is easy to verify. The other requires real security testing.

Compliance Creates False Confidence
Passing audits shifts thinking in the wrong direction.
- Leadership assumes risk is handled
- Security budgets shrink
- Teams stop improving defenses
This is dangerous.
Compliance frameworks lag behind attackers. By the time a method appears in regulations, attackers have already evolved.
Where Traditional DLP Fails
1. Pattern Matching Misses Critical Data
Most DLP tools rely on patterns:
- Credit card numbers
- Social Security numbers
- Defined formats
But your most valuable data rarely fits patterns.
Examples:
- Source code
- Product roadmaps
- Business strategies
- Customer conversations
These pass through DLP undetected.
2. Shadow IT and Encrypted Channels Bypass Controls
Employees don’t always use approved tools.
Common gaps:
- Personal email on mobile
- Cloud storage outside IT visibility
- Messaging apps with encryption
Even when DLP correctly identifies sensitive content, attackers still bypass controls using encrypted channels and shadow IT, creating blind spots that traditional security tools cannot monitor.
DLP only monitors approved channels. Attackers use everything else.
3. Insider Threats Go Undetected
The hardest threat is internal.
- Employees already have access
- No policy violation at first
- Data access looks normal
Example:
A sales manager downloads customer data before leaving.
No alert triggers. No rule is broken.
Traditional DLP cannot detect intent. It only detects patterns.

The Hidden Risk: Alert Fatigue
Too Many Alerts, Too Little Action
DLP systems generate noise.
- Thousands of alerts daily
- Most are false positives
- Analysts ignore alerts over time
Result:
Real threats get buried.
Data is already gone before investigation starts.
Strict Policies Create Workarounds
When controls block work, people bypass them.
- USB blocked → use personal devices
- Email restricted → take photos of screens
- File sharing blocked → use private apps
Security creates friction. Users find alternatives.
What Works Better Than Traditional DLP
1. Behavioral Analytics (UEBA)
Behavior tells you more than patterns.
UEBA tracks:
- Normal user activity
- File access habits
- Data transfer volumes
It flags anomalies like:
- Sudden bulk downloads
- Access outside normal hours
- Unusual file transfers
This detects insider threats early.
2. Data-Centric Security
Instead of protecting systems, protect the data itself.
Key methods:
- File-level encryption
- Access control inside documents
- Usage restrictions after download
Even if data leaves your network, it stays protected.
This approach fits modern environments:
- Remote work
- Cloud platforms
- Third-party sharing
How to Build a Real Data Protection Strategy
Focus on both compliance and actual security.
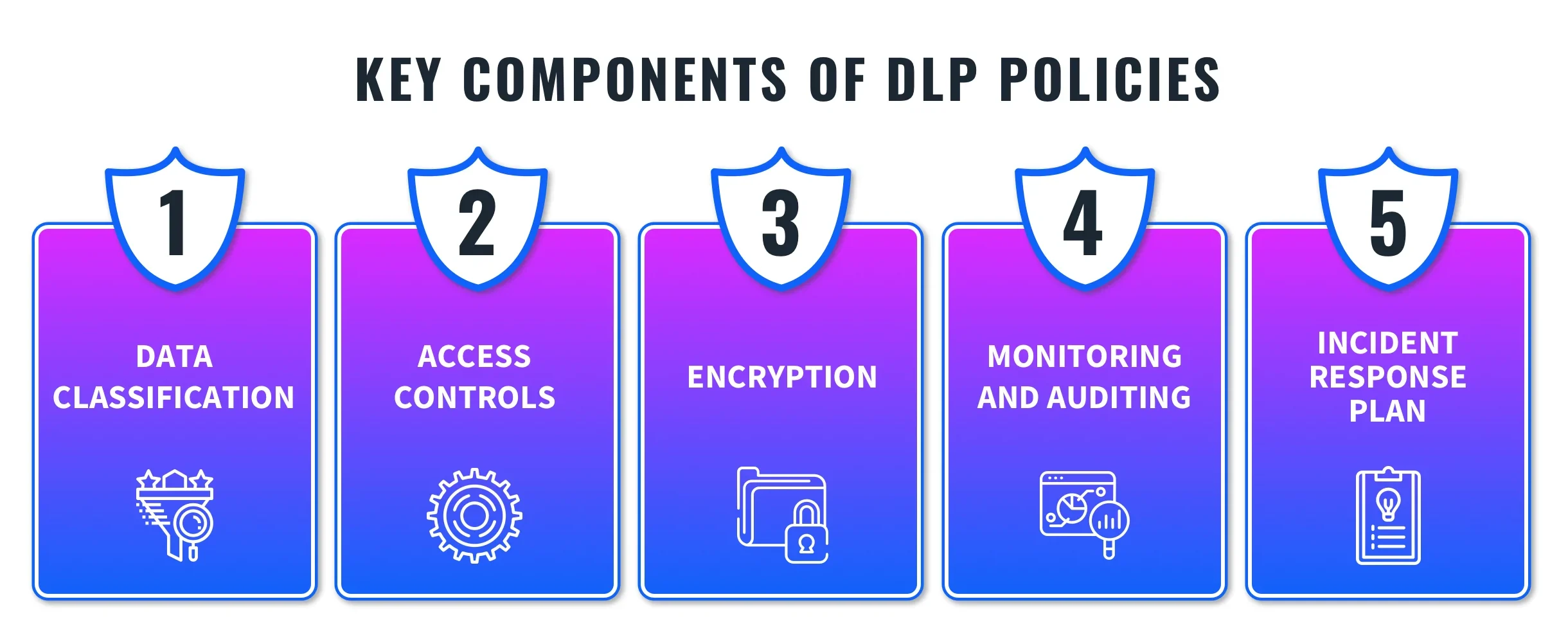
Step 1: Identify Critical Data
Know what matters most:
- Intellectual property
- Customer data
- Financial records
Map where it lives and how it moves.
Step 2: Combine DLP With Behavior Monitoring
Do not rely on rules alone.
- Use DLP for known risks
- Use UEBA for unknown threats
This closes detection gaps.
Step 3: Apply Persistent Protection
Protect data beyond your network.
- Restrict copying
- Control sharing
- Limit access by user and device
Even leaked files stay unusable.
Final Thought
Compliance proves you followed rules.
Security proves you stopped threats.
You need both, but they are not the same.
If your strategy ends at passing audits, your data is still at risk.
Also Visit: JustDone Ai